Getty Photographs
In the event you’re utilizing Amazon Net Companies and your S3 storage bucket might be reached from the open internet, you’d do nicely to not choose a generic title for that area. Keep away from “instance,” skip “change_me,” do not even go together with “foo” or “bar.” Another person with the identical “change this later” pondering can price you a MacBook’s value of money.
Ask Maciej Pocwierz, who simply occurred to select an S3 title that “one of many standard open-source instruments” used for its default backup configuration. After organising the bucket for a consumer challenge, he checked his billing web page and located almost 100 million unauthorized makes an attempt to create new recordsdata on his bucket (PUT requests) inside at some point. The invoice was over $1,300 and counting.
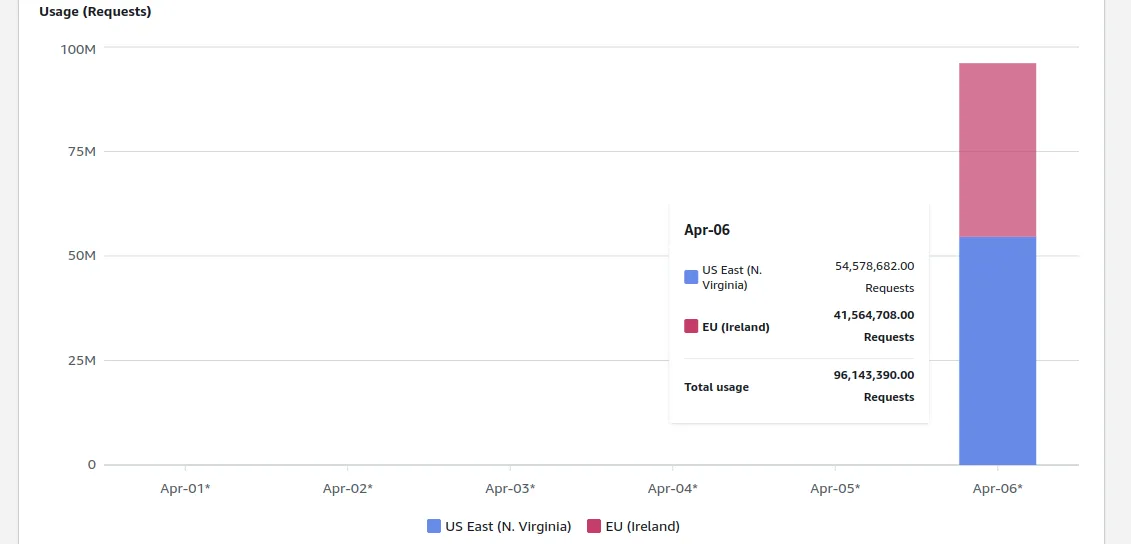
Nothing, nothing, nothing, nothing, nothing … almost 100 million unauthorized requests.
“All this truly occurred only a few days after I ensured my consumer that the worth for AWS providers will probably be negligible, like $20 at most for your entire month,” Pocwierz wrote over chat. “I defined the scenario could be very uncommon but it surely undoubtedly seemed as if I did not know what I am doing.”
Pocwierz declined to call the open supply software that inadvertently bum-rushed his S3 account. In a Medium put up concerning the matter, he famous a distinct downside with an unfortunate default backup. After turning on public writes, he watched as he collected greater than 10GB of information in lower than 30 seconds. Different individuals’s information, that’s, and so they had no concept that Pocwierz was amassing it.
A few of that information got here from firms with clients, which is a part of why Pocwierz is maintaining the specifics beneath wraps. He wrote to Ars that he contacted a few of the firms that both tried or efficiently backed up their information to his bucket, and “they fully ignored me.” “So now as a substitute of getting this fastened, their information continues to be in danger,” Pocwierz writes. “My lesson is that if I ever run an organization, I’ll undoubtedly have a bug bounty program, and I’ll deal with such warnings severely.”
As for Pocwierz’s accounts, each S3 and financial institution, it largely ended nicely. An AWS consultant reached out on LinkedIn and canceled his invoice, he mentioned, and was instructed that anyone can request refunds for extreme unauthorized requests. “However they did not explicitly say that they may essentially approve it,” he wrote. He famous in his Medium put up that AWS “emphasised that this was executed as an exception.”
In response to Pocwierz’s story, Jeff Barr, chief evangelist for AWS at Amazon, tweeted that “We agree that clients shouldn’t should pay for unauthorized requests that they didn’t provoke.” Barr added that Amazon would have extra to share on how the corporate might stop them “shortly.” AWS has a short explainer and speak to web page on sudden AWS expenses.
The open supply software did change its default configuration after Pocwierz contacted them. Pocwierz instructed to AWS that it ought to limit anybody else from making a bucket title like his, however he had but to listen to again about it. He suggests in his weblog put up that, past random dangerous luck, including a random suffix to your bucket title and explicitly specifying your AWS area might help keep away from large expenses just like the one he narrowly dodged.